DMS - Unified Modelling Language¶
12/10/20¶
UML: A specification defining a graphical language for visualising, specifying, constructing and documenting the artefacts of distributed object systems.
Latest version: 2.6
Benefits of UML
- Enhances communication and ensures the right communication
- Captures the logical software architecture independent of the implementation language.
- Helps to manage the complexity
- Enables reuse of design

Object Orientated Analysis¶
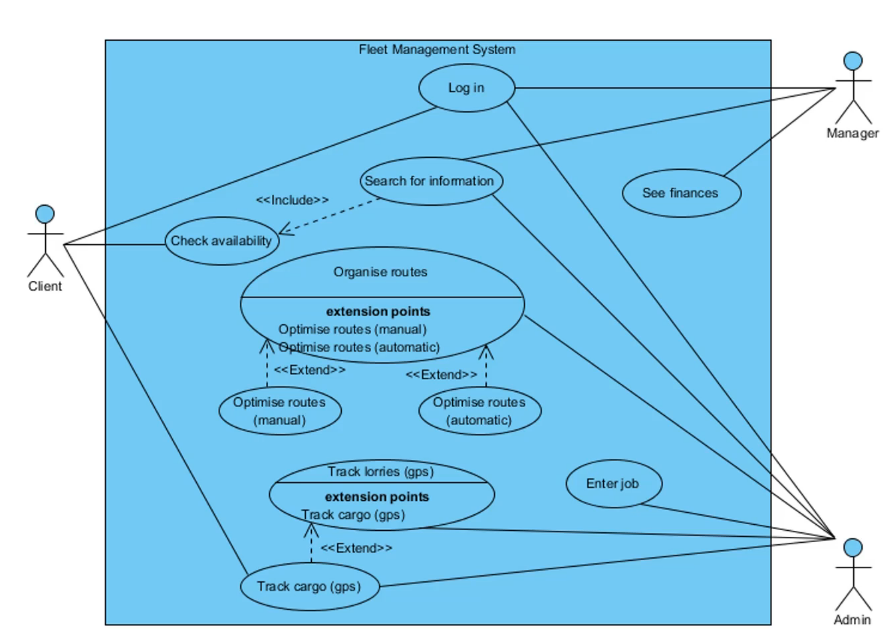
Use case diagrams
- Describe a set of actions that some system should or can perform in collaboration with one or more external users of the system.
- No attempt to represent an order or a number of executions.
Use case diagram components
Actors - Entities that interface with the system. Can be people or other systems.
Use case - Based on user stories and represent what the actor wants your system to do for them. In the use case diagram only the use case name is represented.
Subject - Classifier representing a business, software system, physical system or device under analysis design, or consideration.
Relationships
Relationships between use case and actor
- Association indicates which actor indicates which use case
Relationship between two use cases
- Specifying common functionality and simplifying use case flows
- Using <
> or < >
<<include>>- multiple use cases share a piece of same functionality which is placed in a separate use case.
<<extend>> - Used when activities might be performed as part of another activity but are not mandatory for a use case to run successfully.
Use case diagram of a fleet logistics management company
Base Path - The optimistic path (best case scenario)
Alternative Path - Every other possible way the system can be used/abused. Includes perfectly normal alternate use, but also errors and failures.
Use Case: Borrow copy of book
Purpose: The book borrower (BB) borrows a book from the library using the Library Booking System (LBS)
Pre-conditions:
- The book must exist
- The book must be available
Base Path:
- LBS requests membership card
- BB provides membership card
- BB is logged in by LBS
- LBS checks permissions / debts
- LBS asks for presenting a book
- BB presents a book
- LBS scans RFID tag inside book
- LBS updates records accordingly
- LBS disables anti-theft device
- BB is logged out by LBS
- LBS confirms that process has been completed successfully
Alternative Path
- BB's card has expired: Step 3a: LBS must provide a message that card has expired; LBS must exit the use case
Post conditions for base path
Base path - BB has successfully borrowed the book & system is up to date.
Alternate Path 1 - BB was NOT able to borrow the book & system is up to date.